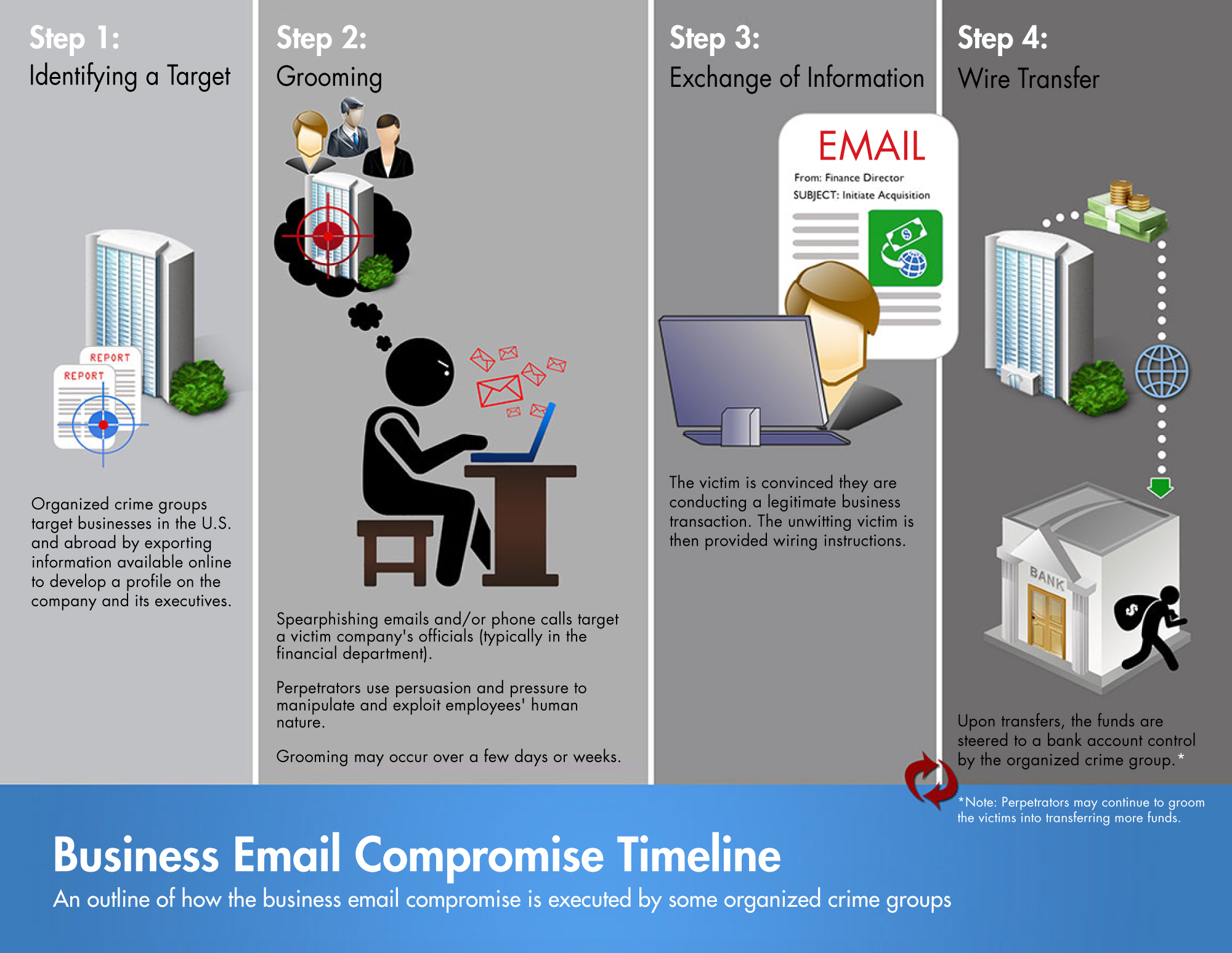
Business Email Compromise (BEC) is a type of cybercrime that involves an attacker using email to deceive victims, usually for financial gain. The criminal impersonates an executive, vendor, customer, or trusted third party and sends messages to employees with access to corporate finances. The attacker then requests wire transfers or leverages the trust of an individual to gain access to sensitive corporate information.
BEC scams are becoming increasingly sophisticated. Attackers use detailed tactics such as gathering information on the target’s activities from publicly available sources, or conducting background research into the target company before submitting the malicious email. Attackers may even send an email from an address that looks like it is a legitimate account within the target organization, lending an additional layer of credibility.
Victims of BEC attacks often face significant financial losses and the loss of sensitive data. The FBI reported that in the first quarter of 2020 alone, BEC scams resulted in total losses of over $2 billion.
BEC scams are typically prevented by educating users on security-awareness best practices and implementing strong authentication methods. For example, users should always look out for typos, unfamiliar addresses, and suspicious requests. Furthermore, businesses can implement strategies such as email authentication, threat management services, and incident response plans to protect against BEC scams. By implementing these measures, organizations can significantly reduce their risk of falling victim to BEC attacks.