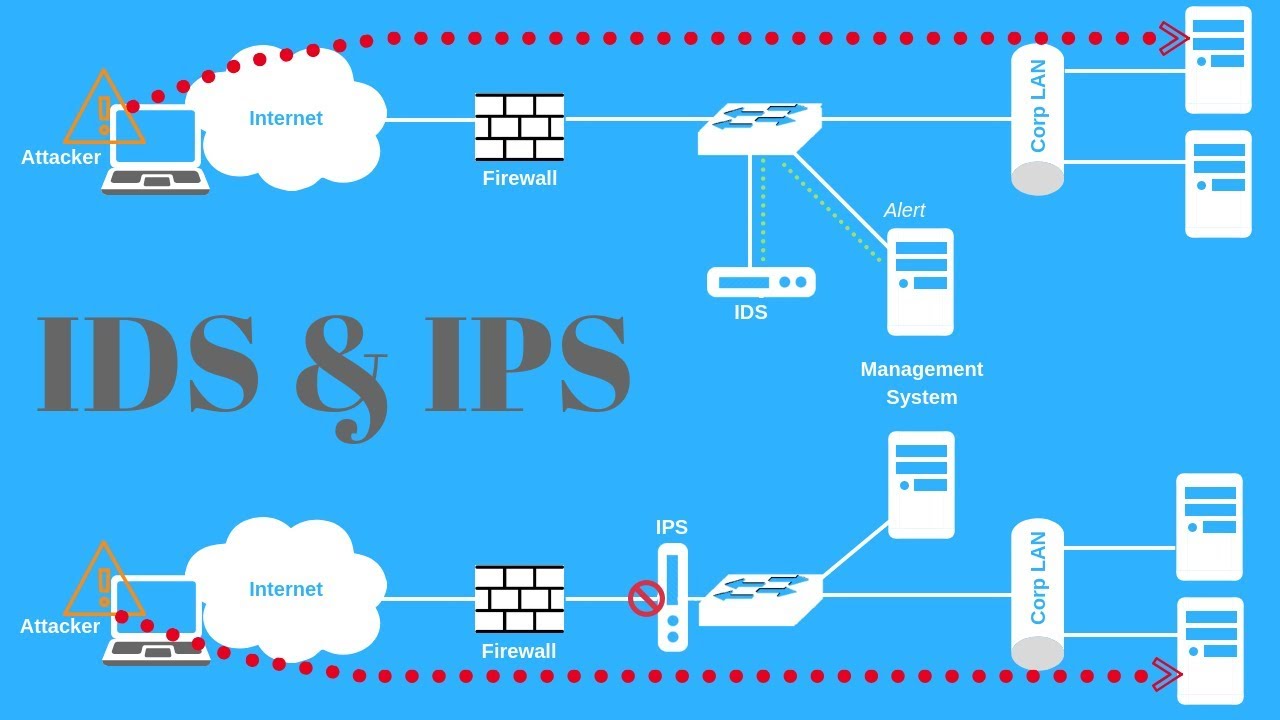
Intrusion Prevention System (IPS) is an important component of an organization’s cybersecurity efforts. It is a layer of defense that scans incoming and outgoing traffic to stop malicious activities, such as illegal access or denial of service attacks, on an organization’s network. IPS systems are usually configured to detect and block data packets that contain particular characteristics associated with malicious functions.
IPS works by monitoring network activity and evaluating behaviors associated with malicious activity. It can typically detect a wide range of malicious behavior, such as IP address spoofing, protocol misuse, buffer overflow, SQL injection, worm scanning, and more. When an attack is detected, the IPS system takes appropriate action, such as blocking the connection, logging an alert and sending an email notification.
Generally, IPS solutions are useful for all types of organizations, keeping their networks secure from a variety of threats. It is important to note that an IPS is not a substitute for other security strategies, such as a firewall or regular patch management. Ideally, an IPS should work in conjunction with other security measures to ensure the best level of protection possible for an organization’s network and data.