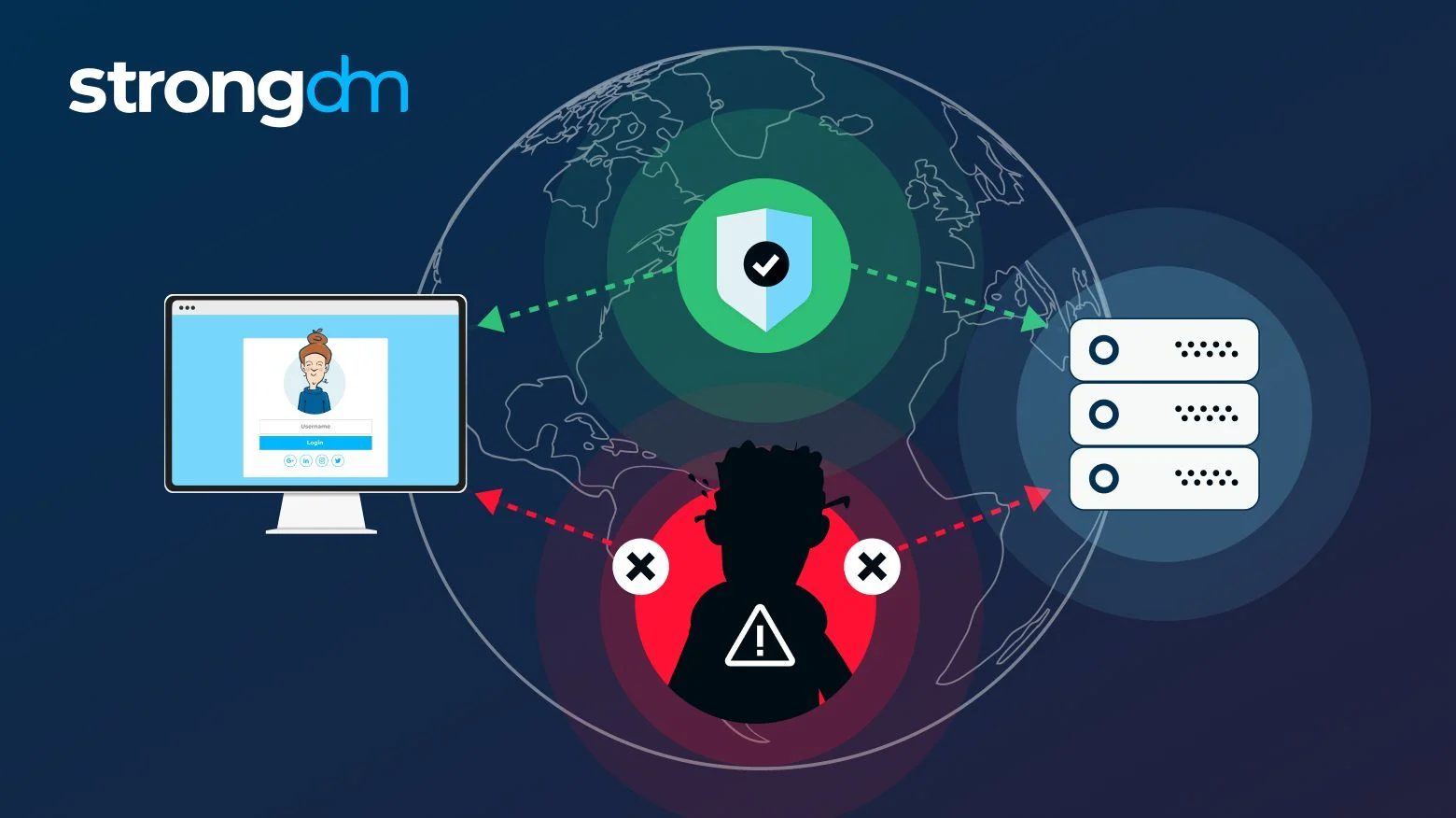
Man-in-the-Middle (MitM), also known as a “Bucket Brigade Attack”, is a type of cyberattack in which the attacker is able to intercept and modify traffic between two parties without either of them knowing. This allows the attacker to eavesdrop on the communications and potentially manipulate the data passing between them. A man-in-the-middle attack can be used to intercept login credentials, passwords, financial information, communications, or other sensitive data.
The basic concept of a MitM attack is that the attacker uses a technique known as “spoofing”, wherein they can masquerade as either of the two parties communicating with each other. The malicious actor is therefore able to decrypt and modify the data going back and forth, without either side knowing about it. MitM attacks can be performed over a network or on individual devices, and can also be used to gain control of systems or accounts.
Protecting against man-in-the-middle (MitM) attacks is a multi-faceted approach depending on the target of the attack. For network-level MitM attacks, firewalls and network monitoring tools can help detect early warning signs of an attack. On the device level, users can take measures such as using strong passwords and multifactor authentication to protect themselves. End-to-end encryption is also a key form of protection, since it helps ensure that the data being sent is secure.
Ultimately, the best approach to secure yourself against MitM attacks is to always be aware of the risks associated with using public networks or computers, and to always be sure to use secure internet connections, such as VPNs, when available.