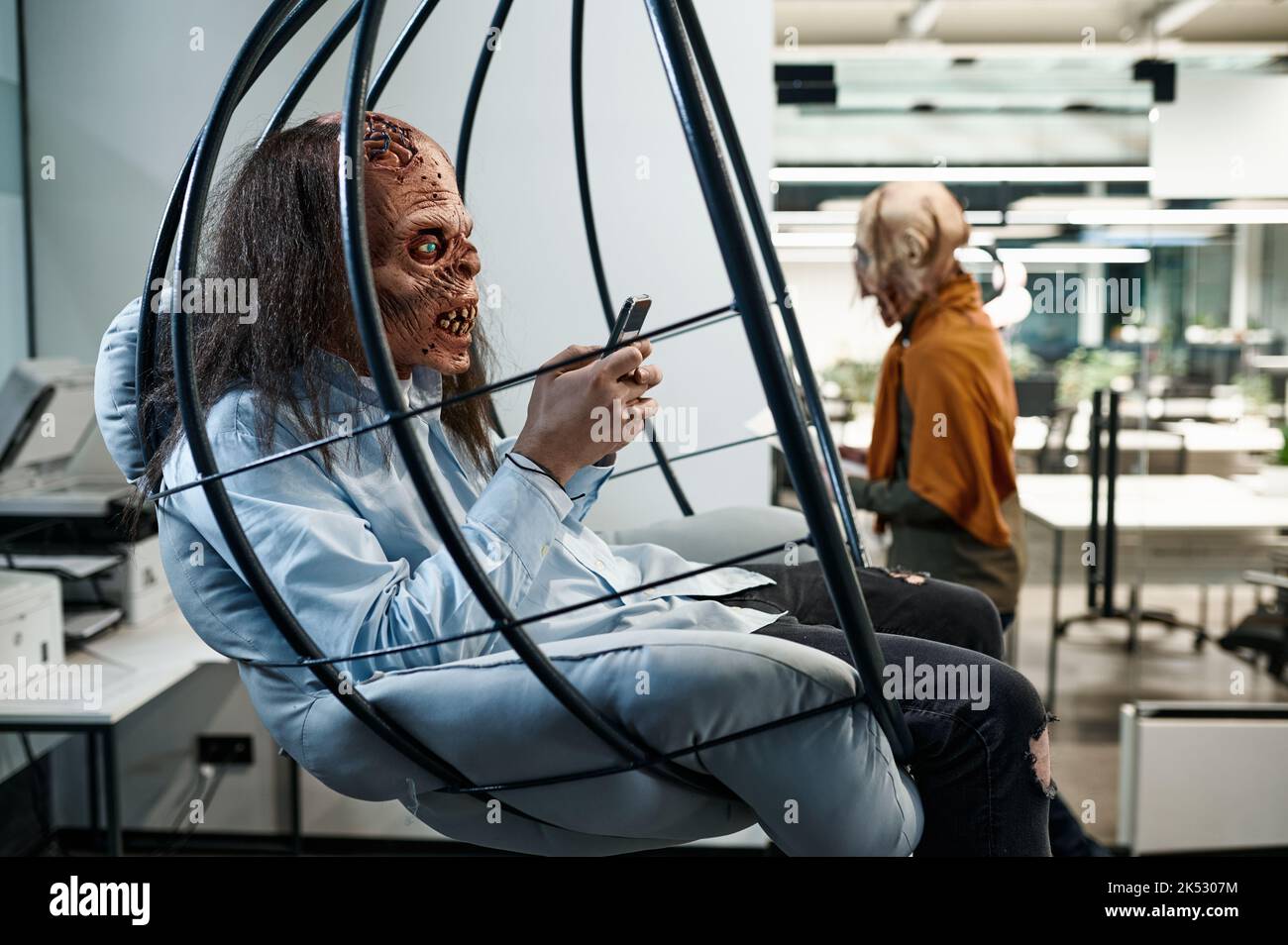
Zombie Network, also known as a “Botted Network,” is a term to describe a large group of computers that have been compromised by malicious software. These computers are often referred to as “zombies” because they have been infected without the owners’ knowledge or consent.
A zombie network is created when a malicious hacker takes control of a computer using a virus or worm. This “master” then uses the zombie to scan for other vulnerable computers on the internet, and infects those as well. The attacker can use these computers to launch distributed denial-of-service (DDoS) attacks, send spam, steal data, or use them as proxies to access restricted services.
Identifying a zombie network can be difficult because the computers often appear to be legitimate users and can have normal network loads. In some cases, security software or a manual review of the network traffic can reveal the zombie network. Additionally, some organizations use honeypots or honeynets to monitor Internet traffic to detect the presence of zombie networks.
Zombie networks can be prevented by keeping systems secure with up-to-date anti-virus software, using strong passwords, and avoiding clicking on suspicious links or downloads.